All articles containing the tag [
Examples
]-
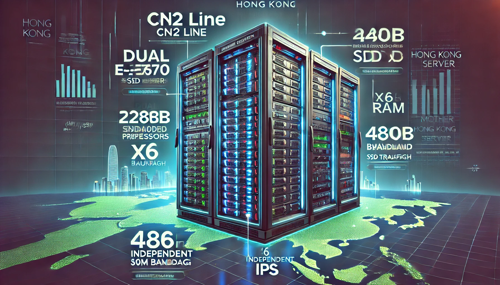
Hong Kong Site Group Server Post Template Examples And Content Layout Strategies Help Increase Rankings
introducing hong kong server post template examples and content layout strategies, covering template structure, meta tags, text layout, internal links and localization optimization, to help improve search rankings and user experience.
Hong Kong Station Group Server Post Template Layout Strategy Seo Localization -
E-commerce Websites Recommend Which Brand Of Japanese Server Is Best To Support Large Traffic And Stable Options
e-commerce website recommendation: which brand of japanese server is good? this article analyzes stable options for large traffic, covering performance, bandwidth, expansion and operation and maintenance support, to help webmasters make the right choice.
Japanese Server E-commerce Website Large Traffic Stability Server Brand Hosting Cdn Elastic Expansion -
Social Media And Kol Are Combined To Teach You How To Build A Korean E-commerce Website And Start Word-of-mouth Communication.
practical guide: combining social media and kol to teach you how to create word-of-mouth communication in korean e-commerce sites. it includes executable steps such as platform selection, kol screening, content strategy, site group optimization and effect monitoring.
Korean E-commerce Website Group Social Media Kol Word-of-mouth Communication Korean Localization E-commerce Promotion Seo Geo Kol Marketing -
Deployment Tutorial Taiwan Cdn Cn2 Access Steps And Common Configuration Examples
detailed deployment tutorial: taiwan cdn cn2 access steps and common configuration examples, covering pre-preparation, network planning, dns/ssl, cache and return-to-origin settings, verification and monitoring, suitable for engineers and operations who want to optimize the access experience in taiwan.
Taiwan Cdn Cn2 Access Deployment Tutorial Cdn Configuration Example Taiwan Acceleration Cn2 Routing Dns Configuration Cache Strategy -
Backup Recovery Strategy And Data Protection Configuration Example For German Vps Server Hosting
this article introduces practical backup and recovery strategies and data protection configuration examples for german vps server hosting, covering backup types, compliance requirements, off-site backup, recovery drills and monitoring, etc., to facilitate the implementation of reliable data protection solutions in the german/eu environment.
German Vps Vps Server Hosting Backup And Recovery Data Protection Disaster Recovery Off-site Backup Snapshot Encrypted Transmission Gdpr -
Developer-only Tutorial: How To Enter Ssh Vpn On Singapore Server And Detailed Instructions On Port Mapping
practical tutorial for developers: secure access via ssh and vpn on a singapore server, and explains common port mapping and tunneling solutions, including scenarios and security suggestions.
Singapore Server Sshvpn Port Mapping Tutorial Developer Remote Access Tunnel Wireguardopenvpnssh Port Forwarding -
Industry Application Perspective Japanese Vps Video Tutorial Practical Guide For E-commerce And Games
from the perspective of industry application, this article systematically explains the key points of deployment, performance optimization, security and operation and maintenance of japanese vps in e-commerce and gaming scenarios. in conjunction with the video tutorial path, executable practical guidance and suggestions are provided.
Japanese Vps Vps Video Tutorial E-commerce Vps Game Server Latency Optimization Deployment Practice Bandwidth Management Security Reinforcement Operation And Maintenance Monitoring Japanese Node -
Detailed Graphic Tutorials And Configuration Examples For Building V2ray On Alibaba Cloud Hong Kong Server
detailed graphic tutorials and configuration examples for setting up alibaba cloud hong kong server v2ray, covering preparation work, system environment, installation commands, configuration file examples, client settings and common troubleshooting, suitable for operation and maintenance and personal use reference.
Alibaba Cloud Hong Kong Server V2ray Setup Tutorial Configuration Instance Installation Configuration Guide Security Group Tls -
Interpret Common Terms And Conditions In Industry Standards And Us Server Hosting Charging Standards
professional interpretation of common terms and conditions in industry standards and us server hosting charging standards, covering billing structure, bandwidth and traffic, sla, contract and termination, technical support, additional fees and billing dispute resolution suggestions.
Us Server Hosting Hosting Charging Standards Industry Specifications Bandwidth Billing Sla Billing Terms